Supporting BYOK Within AWS With Fornetix VaultCore
Amazon Web Services (AWS) is a secure cloud services provider that delivers compute, network, and data storage services. There are numerous benefits to migrating data storage and management to the cloud, but there are security considerations that must be addressed prior to doing so.
When it comes to securing the data stored within AWS, a critical decision will be about encryption and how you plan to manage your encryption keys. You will need to choose where you store your keys, who has access to them, and who controls the life cycle of the keys. Do you want AWS, or any of your cloud providers, to be creating and controlling encryption keys for all data you store in the cloud?
When it comes to encryption key management within AWS, there are two different options supported within each account:
- Amazon provide an offering they call AWS Key Management Service (AWS KMS) to AWS users. AWS KMS creates and stores the master key and all of your keys. It will keep track of your keys and manage access to each object within any given account. This sounds like a safe and convenient way to manage the keys, doesn’t it? Well, this assumes a great trust and faith in your cloud provider. They would control all of your keys and the master key. Amazon will provide the necessary transaction reports so you can keep track of what is happening.
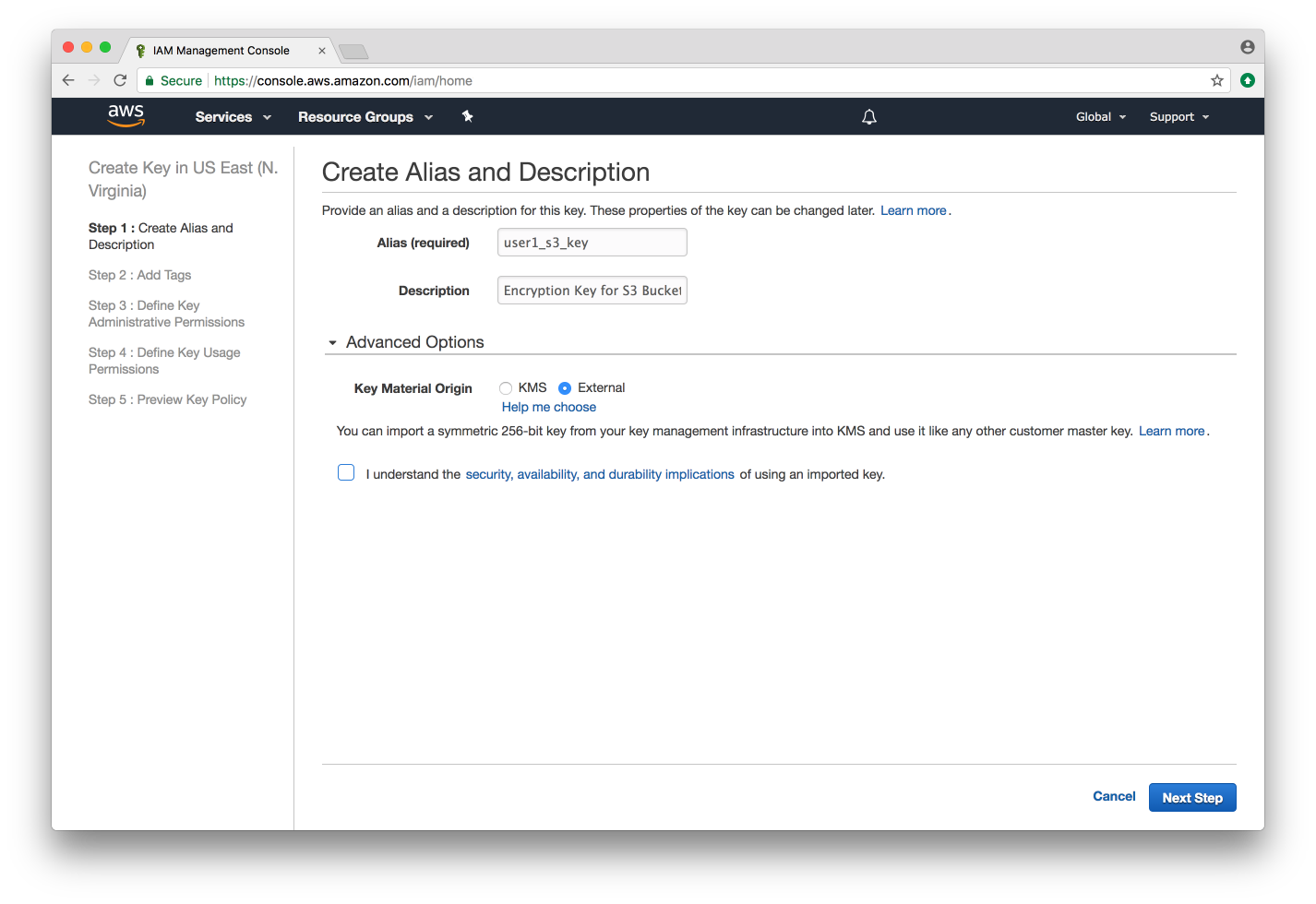
- Users can leverage the Bring Your Own Key (BYOK) functionality within AWS KMS. As seen in the image below, AWS gives you the option to import a AES-256 key to use for encrypting and decrypting your data. When choosing this option, all of the imported encryption keys are backed by a master key provided by a third-party. This option could be driven by a compliance or regulation requirement that requires you to control your keys, or because your organization prefers a unified approach to key management and manages all encryption keys across the enterprise within one application.
The second scenario does have its challenges. What if your keys are lost or stolen? If you lose your key, you will no longer have access to the data that was encrypted by that key. Amazon has no way decrypting your data without that key. Additionally, the manual process of creating and importing a key throughout the BYOK process is one that cannot scale when you’re planning on applying this methodology across an entire enterprise which may be leveraging 100’s of AWS accounts, with 1,000’s of objects within those accounts.
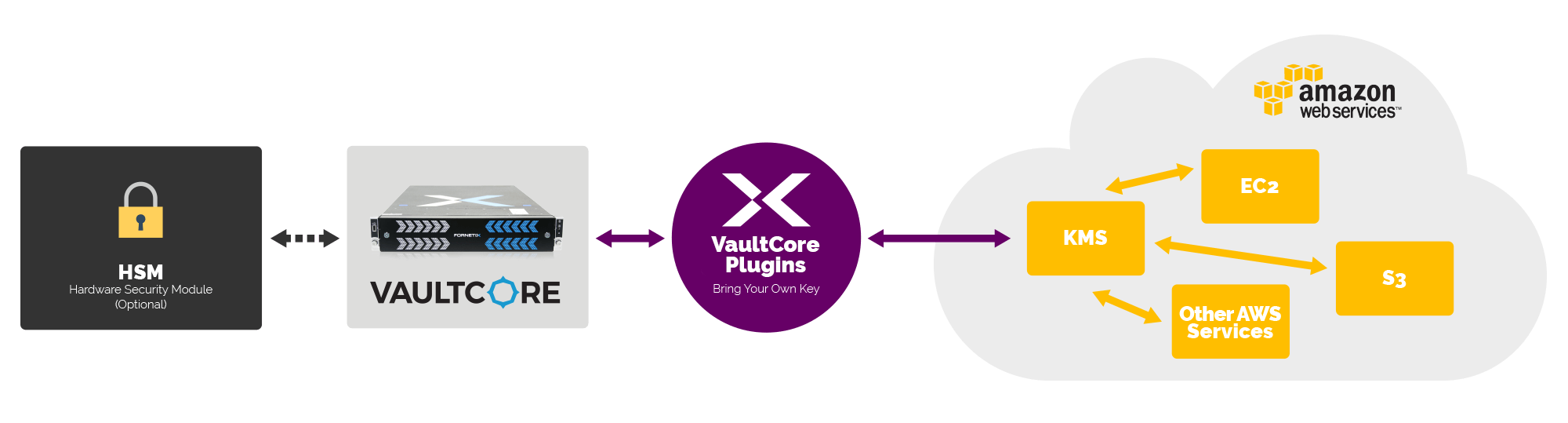
If your organization has chosen BYOK, the best way to easily and quickly implement it is by leveraging a third-party Key Management Server (KMS), like Fornetix VaultCore, that has developed a seamless integration directly with AWS KMS allowing for easy creation, destruction, and reporting of encryption keys being used by AWS.
- 5-minute integration establishes the relationship between AWS KMS and Fornetix VaultCore.
- VaultCore drives creation of encryption keys for use by AWS account holders on a per account based through bulk import giving users immediate access to keys.
- VaultCore has the ability to revoke encryption keys, so AWS accounts are unable to access data using these keys should a situation where this is needed arise.
This is just one example of how companies are leveraging Fornetix to manage the lifecycle of their encryption keys. A commitment to industry standards and interoperability allows Fornetix to bring powerful encryption management to virtually any device or technology.
Are you ready to see how AWS KMS and VaultCore are automating BYOK? Request a custom demo today.
Note: This entry has been edited to reflect the ‘Key Orchestration’ solution name becoming ‘VaultCore’