Guide to Enterprise Key Management (Why Companies Need Key Management)
With large-scale data breaches on the rise in the last few years, affecting millions of people, making sure your company’s sensitive information is safely encrypted and thus secure should be one of your top priorities. Encryption across your organization scales quickly — from securing file-servers to protecting user data — meaning that you could be looking at hundreds if not thousands of encryption keys. This is a lot of information for your team to handle, especially considering the importance of secure and properly managed keys. That’s where enterprise key management comes in.
What Are Enterprise Key Management Solutions?
Key management systems offer a single source for all of an enterprise’s cryptographic keys — character strings that encryption algorithms employ to transform data into random, unrecognizable text. Typically, enterprise key management systems (KMS) have two form factors, virtual or physical appliances. Key management covers the full lifecycle of cryptographic keys, important for protecting sensitive information.
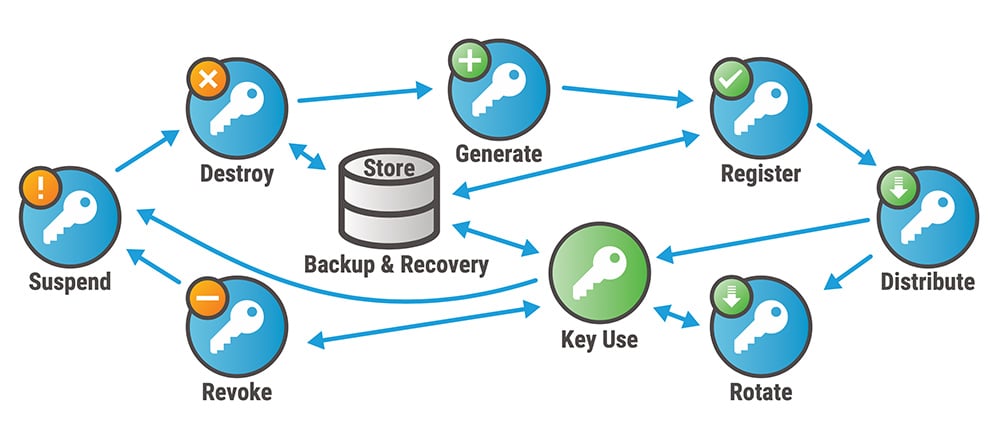
What Is the Enterprise Key Lifecycle?
Encryption keys have a lifecycle, which spans a period of time from creation, through use, and ultimately termination. During this cycle, encryption keys typically go through a number of phases including, generation, activation, storage, rotation, backup, revocation, and then destruction. As mentioned, enterprise key management systems track and control the full lifecycle of each encryption key. Encryption key lifecycles vary depending on the type of key and the key’s operational duration. These factors are determined based on the amount of data being secured and the level of sensitivity.
Why is an Enterprise Encryption Key Management System Necessary?
Newer data and privacy regulations are evolving to include a more granular level of encryption that requires the integration of not only server-level encryption but encryption down to the file level. This granular level of data encryption is creating more keys that prove to be easy targets for bad actors when left unmanaged. To adequately protect the large amount of data being stored and transferred between networks and devices, daily implementation of enterprise key management is essential to the security strategy. Simply put, it cannot be overlooked.
What Are the Benefits of Enterprise Key Management Solutions?
There are several benefits to employing an encryption key management system at your company. From freeing up valuable department time, ensuring continuity of processes, to protection against a data breach, we’ve listed out some of the primary benefits below.
- Automated Backups – Cryptographic key management systems create secure replications of keys to help prevent instances of unexpected key expiration. This also helps minimize key redundancy and ensures the right type of key is being used and rotated accordingly.
- Streamlined Efficiency – With hundreds or even thousands of keys to keep track of, management systems simplify key organization and ensure consolidated data security. This frees up your internal resources to focus on other aspects of your company’s operation and growth.
- Reduced Risk – With automation of policies across your enterprise, you’re guaranteed a high level of security with reduced opportunities for human errors. Key management systems ensure the use of cryptographically strong keys, while protecting against key theft.
- Increased Security – Enterprise key management systems provide secure APIs and communication channels for key distribution and use. They also manage the deletion of keys at the end of their lifecycle, preventing any unexpected security gaps otherwise vulnerable to a data breach.
- Accessibility – Your company’s security administrator can manage, access, and control the key lifecycle from a central point. Gone are the days of hunting and pecking for signed audit logs. A sure asset to meeting new compliance regulations.
- Reduced Cost – Key management systems automate processes at scale, meaning you can eliminate costs related to manual key management. As your company grows, key management systems scale to match your company’s needs. Plus, increased security means reduced costs associated with security breaches from compromised encryption keys.
What Should Your Company Consider Prior to Purchasing an Enterprise Key Management Service?
Before selecting an enterprise key management service for your organization, there are several important things to consider to guarantee you dial in the right solution for your company. Here are a few items you can discuss with a potential enterprise key security provider to confirm the proper protocols are in place:
- Verify that your key manager is FIPS 140-2 certified and can provide you with the certificate number.
- Ask what platforms the management system supports for key retrieval. Are there any gaps in coverage?
- Ask if the key retrieval application interface is common to all platforms.
- Check whether licensing fees are charged separately, for each client operating system, or all at once.
Enterprise Key Management Best Practices
When looking to adopt a key management system, there are a number of things to consider. For example, you want to ensure your encryption key manager is easy to access and that multiple administrators have access to keys in case of emergency. Below are a few more best practices.
- Create encryption key management policies for company employees.
- Support multiple encryption standards.
- Backup your encryption keys and leverage automation.
- Centralize user roles.
- Centralize encryption key management. This keeps everything in one place, and prevents overlaps, duplications, and difficulties.
Ready for expert encryption key management? Contact us today to talk with a Fornetix professional about a custom quote, demo, or any questions you may have.
{{cta(‘c50d7963-7ec6-4e0d-9acf-ffdbc328d35d’)}}